How to Change PowerShell Execution Policies in Windows 11

This guide shows you how to manage PowerShell execution policies on Windows 11. These settings work for both standard Windows PowerShell and PowerShell Core.
Why does Windows 11 block PowerShell scripts by default?
Windows 11 blocks scripts to prevent malicious code from running automatically. This PowerShell security model acts as a barrier, ensuring that only trusted or verified scripts execute. By default, the system prevents unauthorized script execution to protect your computer from potential threats and accidental damage.
What happens when you change the execution policy?
When you modify the execution policy, you alter the rules governing which scripts can run on your system. Changing these settings can either tighten security or open your computer to risks. Always ensure you understand the implications before lowering your security posture.
Understanding PowerShell Execution Policies
Execution policies are not a firewall, but they are a vital part of the PowerShell security model. They determine if you can load configuration files or run scripts. Here are the common modes:
- Restricted: Default setting. No scripts allowed.
- RemoteSigned: Scripts created locally run; downloaded scripts must be signed by a trusted publisher.
- AllSigned: Every script must be signed by a trusted publisher.
- Bypass: Nothing is blocked. Use only for specific, trusted automation tasks.
- Unrestricted: All scripts run. This is a major security risk.
How to Check and Change Policies
To see your current settings, open PowerShell and run: Get-ExecutionPolicy -List. This shows the policy for each ExecutionPolicyScope.
Note: Changing system-wide policies requires Administrator privileges.
To set a policy for the current user, use: Set-ExecutionPolicy RemoteSigned -Scope CurrentUser. To change it for the entire machine, you must run PowerShell as an administrator and use: Set-ExecutionPolicy RemoteSigned -Scope LocalMachine.
Safer Alternatives: Unblock-File
Instead of changing your global policy, you can unblock a specific script. This is a best practice for security. Use this command:
Unblock-File -Path "C:\Scripts\MyScript.ps1"
Troubleshooting and Group Policy
If you receive a PowerShell script error stating that execution is disabled, check if a Group Policy Object (GPO) is enforcing a stricter policy. GPO settings override local changes. You can view GPO-applied policies by checking the registry path: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell.
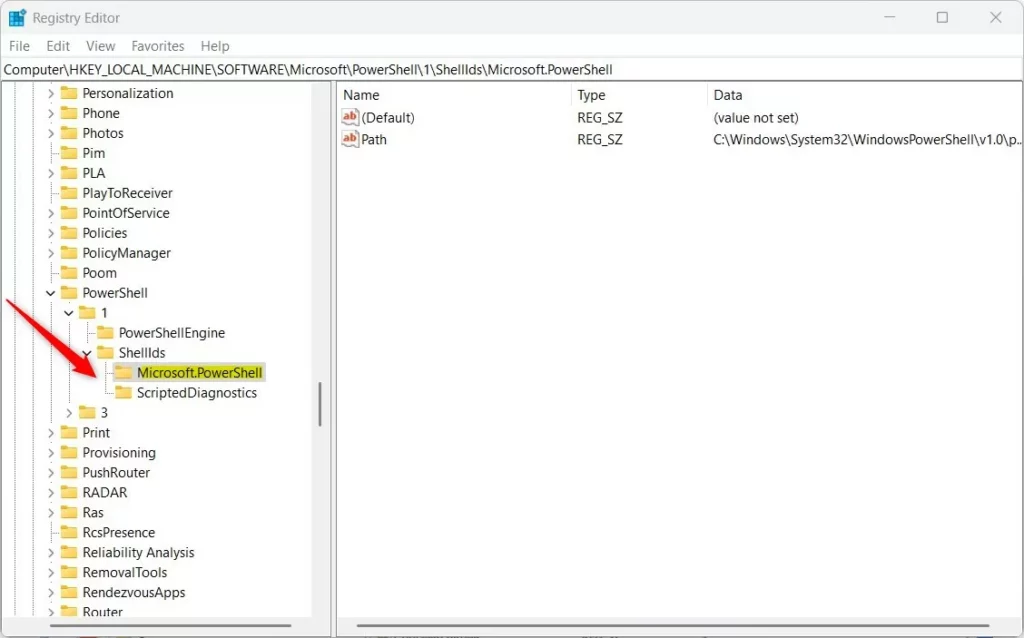
Registry Editor Method
Requires Administrator privileges.
- Open the Windows Registry Editor.
- Navigate to:
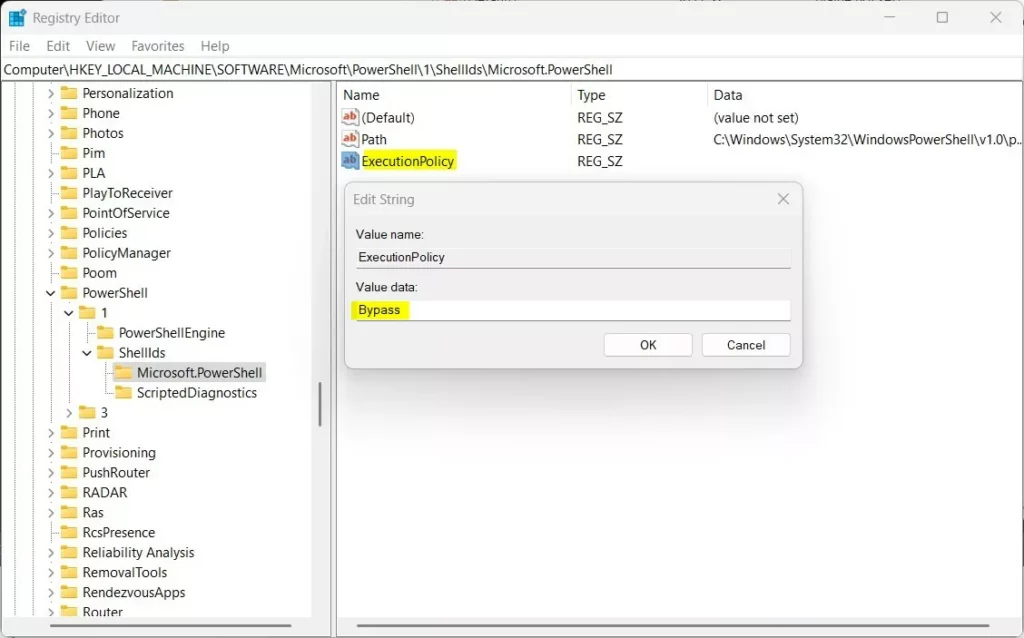
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell - Create a new String Value named
ExecutionPolicy. - Set the value to
RemoteSigned.
Summary
Managing your PowerShell execution policy is essential for Windows 11 security. We covered how to check policies with Get-ExecutionPolicy, how to use Unblock-File for safer script execution, and how to handle GPO overrides. Always prioritize the RemoteSigned policy to keep your system secure while allowing necessary automation. For advanced parameters, refer to the official Microsoft documentation.
Is it safe to set execution policy to Unrestricted?
No, setting your policy to Unrestricted is not safe. It removes all security checks, allowing any script to run on your system. This makes your computer vulnerable to malicious software and unauthorized automation. Always prefer RemoteSigned for a balance of security and functionality.
Was this guide helpful?

Leave a Reply