How to Allow Apps in Windows 11 Controlled Folder Access
This guide shows you how to let specific apps use your protected folders using Microsoft Defender Antivirus in Windows 11.
Understanding Windows 11 Controlled Folder Access
Controlled folder access is a powerful security feature within Microsoft Defender Antivirus. It acts as a gatekeeper for your important files. It prevents unauthorized changes from malicious software, specifically ransomware, which tries to encrypt your data. By monitoring which apps can access protected system folders, it ensures your data security remains intact.
Why do this?
Sometimes, Windows 11 blocks a safe app because it thinks the app is a threat. By adding that app to your allowed list, you tell Windows that the program is safe to use. This keeps your files protected while letting your trusted apps work normally.
What happens when done?
Once you add an app to the list, it can read and write to your protected folders without being blocked. Ransomware will still be blocked by default, keeping your data safe from being locked by hackers.
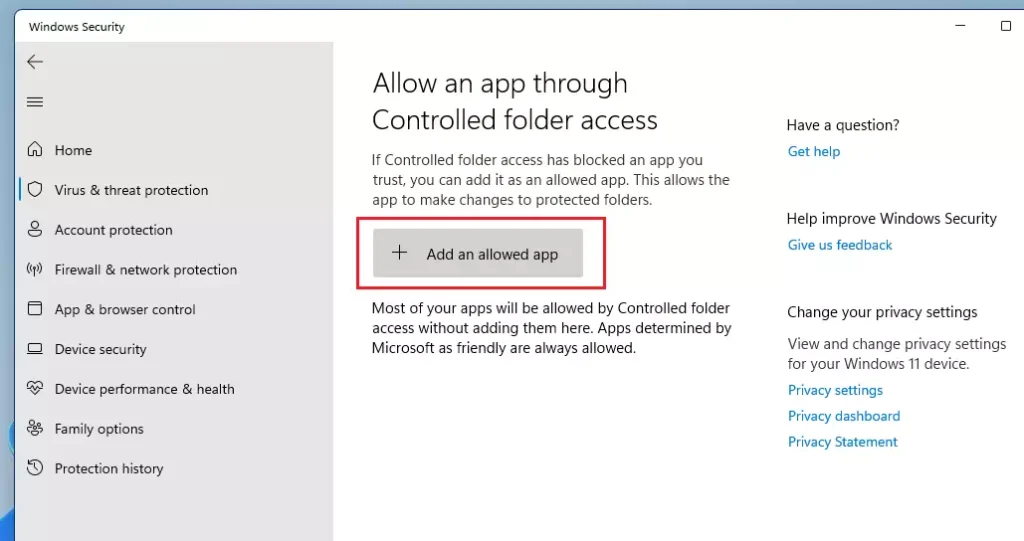
Allowing apps through Controlled folder access
You can add apps that are being blocked by following these steps:
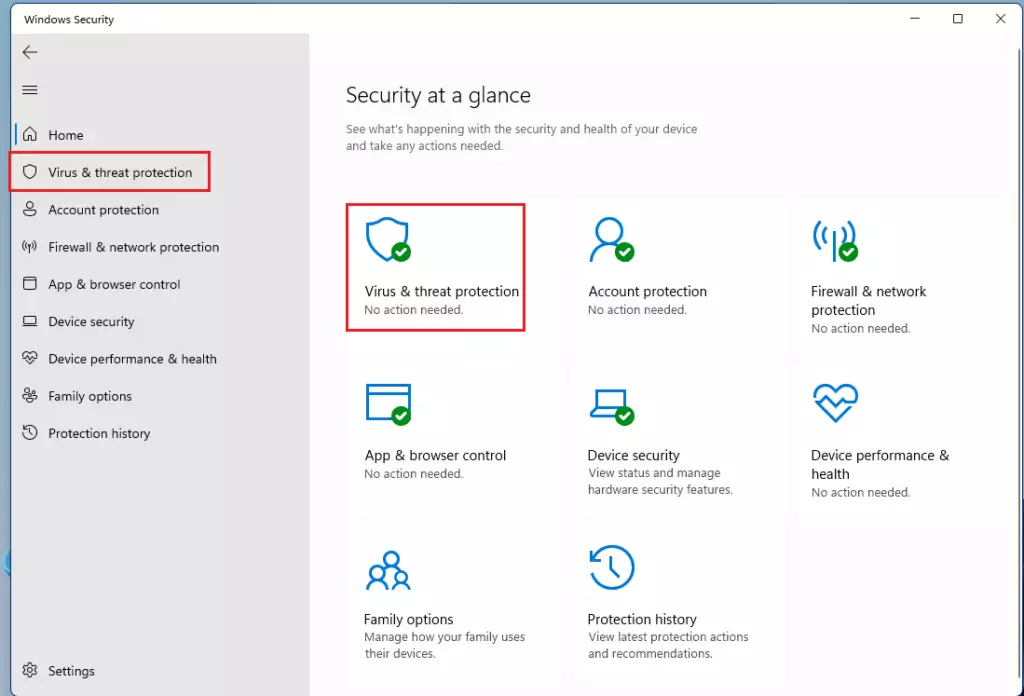
- Click the search box on your taskbar, type Windows Security, and click Windows Security.
- Click Virus & threat protection.
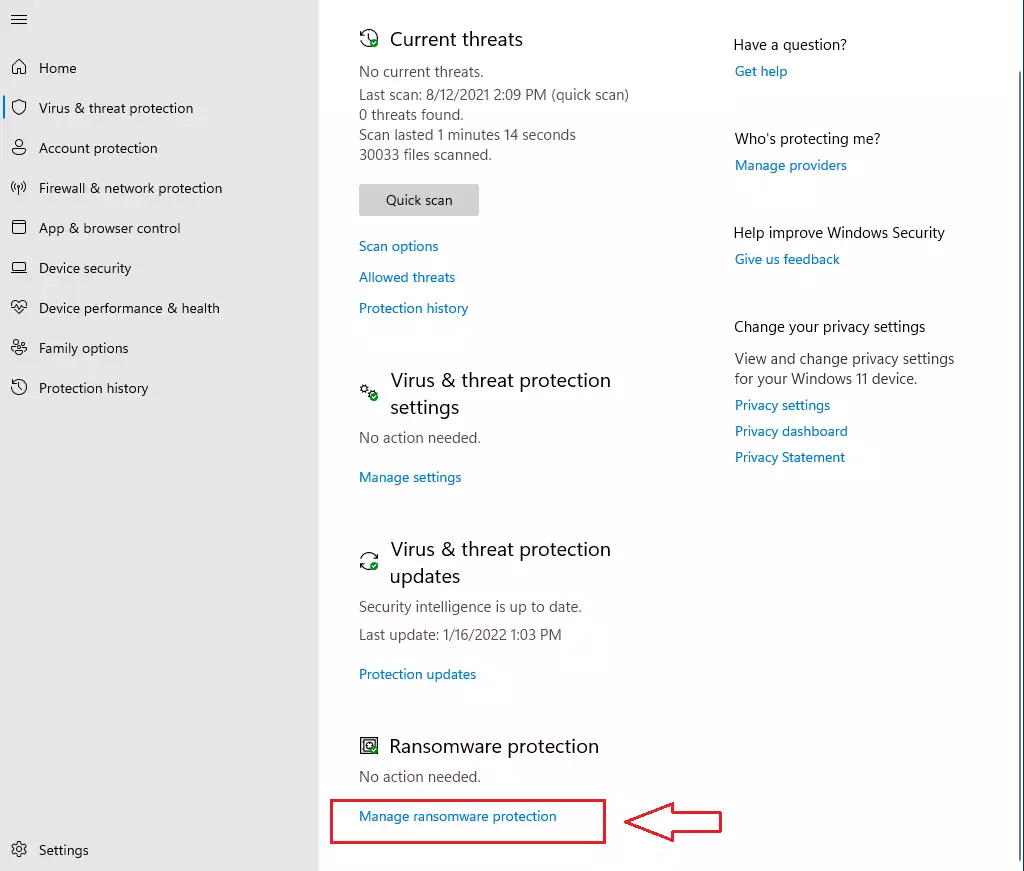
- Look for Ransomware protection and click Manage ransomware protection.
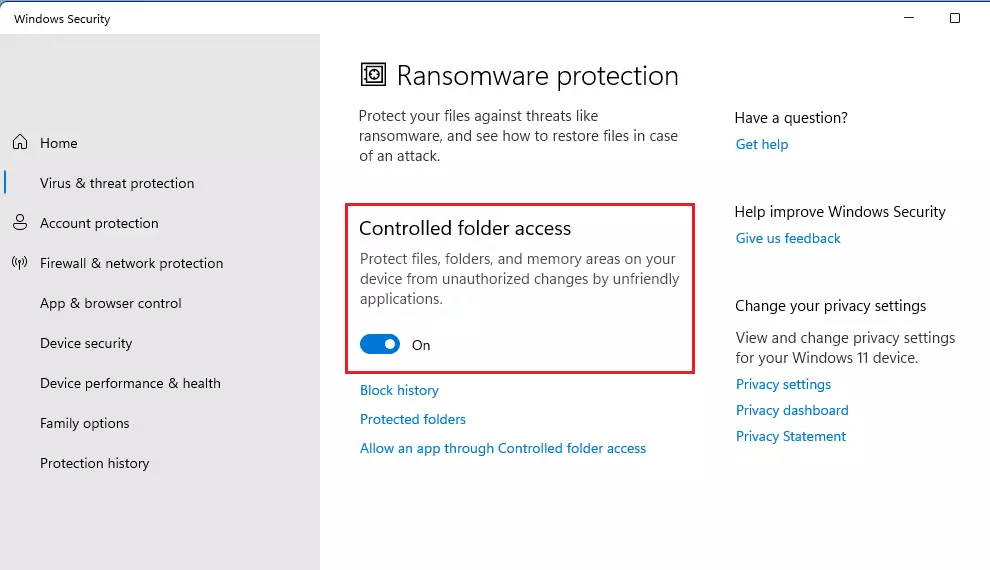
- Make sure Controlled folder access is turned On.
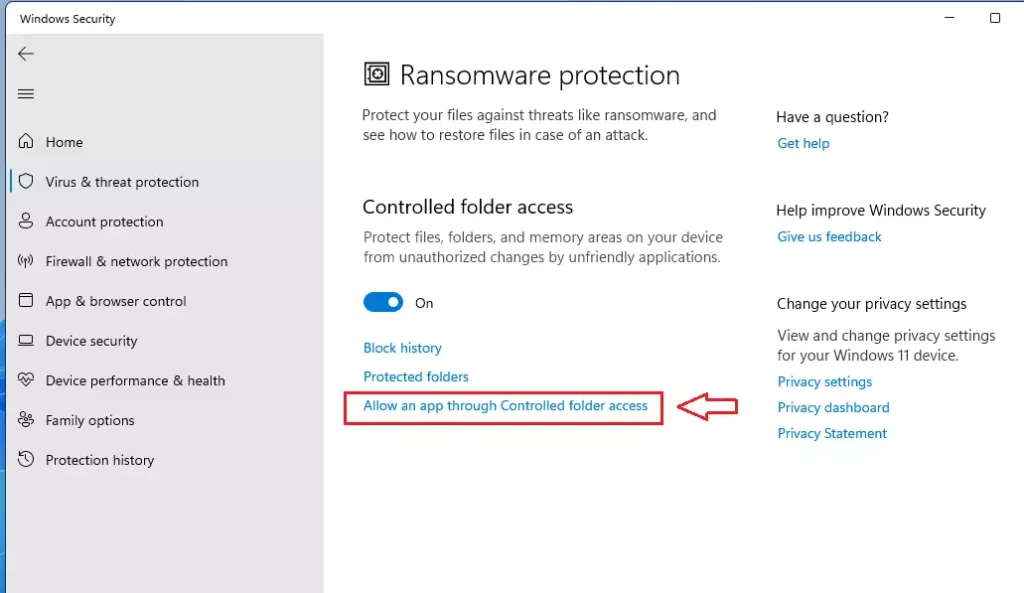
- Click the link that says Allow an app through Controlled folder access.
- Click Add an allowed app. Find the program you want to allow on your computer and click Open.
Managing access with PowerShell (Admin)
Note: This section requires admin privileges.
You can use PowerShell to quickly whitelist applications. Open PowerShell as an administrator and use the following command:
Add-MpControlledFolderAccessAllowedApplication -ApplicationPath "C:\Path\To\Your\App.exe"
This command adds the specified executable to the whitelist, allowing it to bypass the restriction immediately.
Managing access with Registry (Admin)
Note: This section requires admin privileges.
Advanced users can modify the registry to manage allowed apps. Navigate to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Windows Defender Exploit Guard\Controlled Folder Access\AllowedApplications. You can add a new string value here with the full path of your application.
Troubleshooting and Event Viewer
If an app is blocked, you can verify this in the Event Viewer. Navigate to Applications and Services Logs > Microsoft > Windows > Windows Defender > Operational. Look for Event ID 1123. This log entry confirms that an app was blocked by Controlled folder access, helping you identify which programs need to be added to your whitelist.
Enterprise and MDM Deployment
In a business environment, IT administrators use Microsoft Defender for Endpoint and Attack Surface Reduction (ASR) rules to manage these settings across many computers. Using Intune or Group Policy, admins can push a centralized list of allowed applications to ensure consistent threat prevention across the entire organization.
Summary
Controlled folder access is a vital layer of data security. By managing your allowed apps through the GUI, PowerShell, or Registry, you ensure that legitimate software functions correctly while keeping ransomware at bay. Always check the Event Viewer if you suspect a legitimate app is being blocked.
Why is Controlled Folder Access missing or greyed out?
If the option is greyed out, it is likely managed by your organization via Group Policy or Intune. In a home environment, ensure you have administrative rights and that your Windows Security app is fully updated. If a third-party antivirus is installed, it may also disable these native Microsoft Defender features.
Does Controlled Folder Access impact system performance?
Controlled folder access has a negligible impact on system performance for most users. It only monitors write operations to specific protected folders. You will not notice a slowdown during daily tasks, as the security checks happen in the background without requiring significant CPU or memory resources.
Was this guide helpful?
About the Author
Richard
Tech Writer, IT Professional
Richard, a writer for Geek Rewind, is a tech enthusiast who loves breaking down complex IT topics into simple, easy-to-understand ideas. With years of hands-on experience in system administration and enterprise IT operations, he’s developed a knack for offering practical tips and solutions. Richard aims to make technology more accessible and actionable. He's deeply committed to the Geek Rewind community, always ready to answer questions and engage in discussions.


No comments yet — be the first to share your thoughts!