This guide shows you how to turn on or off Kernel-mode Hardware-enforced Stack Protection in Windows 11. This feature helps protect your computer from harmful software.
Core isolation is a Windows security feature. It protects important parts of Windows from malicious software by keeping them separate in your computer’s memory. It does this by running these parts in a special protected environment.
Hardware-enforced Stack Protection provides strong protection against Return Oriented Programming (ROP) exploits. It does this by keeping track of how a program is supposed to run.
The Kernel Mode Hardware Enforced Stack Protection security feature works on Windows 11, version 22H2 and newer versions. It adds extra security for the core code that runs your computer.
How It Works
When code runs deep in your computer’s system, the CPU checks that return addresses are correct. It compares them to a backup copy stored in the shadow stack. This stops attackers from changing an address to run harmful code instead.
What You Need
- CPU: Intel Tiger Lake (11th Gen) or newer with Control-Flow Enforcement Technology (CET), or AMD Zen 3 Ryzen or newer with AMD shadow stacks
- CPU virtualization turned on
- Memory Integrity turned on
Reference: Windows 11, version 22H2 Security baseline | Microsoft Community Hub
Microsoft released a security update package for Windows 11, version 22H2. KB5026372 Build 22621.1702 adds more drivers to a list of drivers that don’t work with Kernel-mode Hardware-enforced Stack Protection. Your computer checks this list when you turn on this feature.
Important: You must be signed in as an administrator to enable or disable this feature. Not all drivers work with Kernel Mode Hardware Enforced Stack Protection.
Option One: Use Windows Security App
Turn Kernel-mode Hardware-enforced Stack Protection On or Off
- Open Windows Security.
- Click Device security on the left side. Then click Core isolation details on the right side.
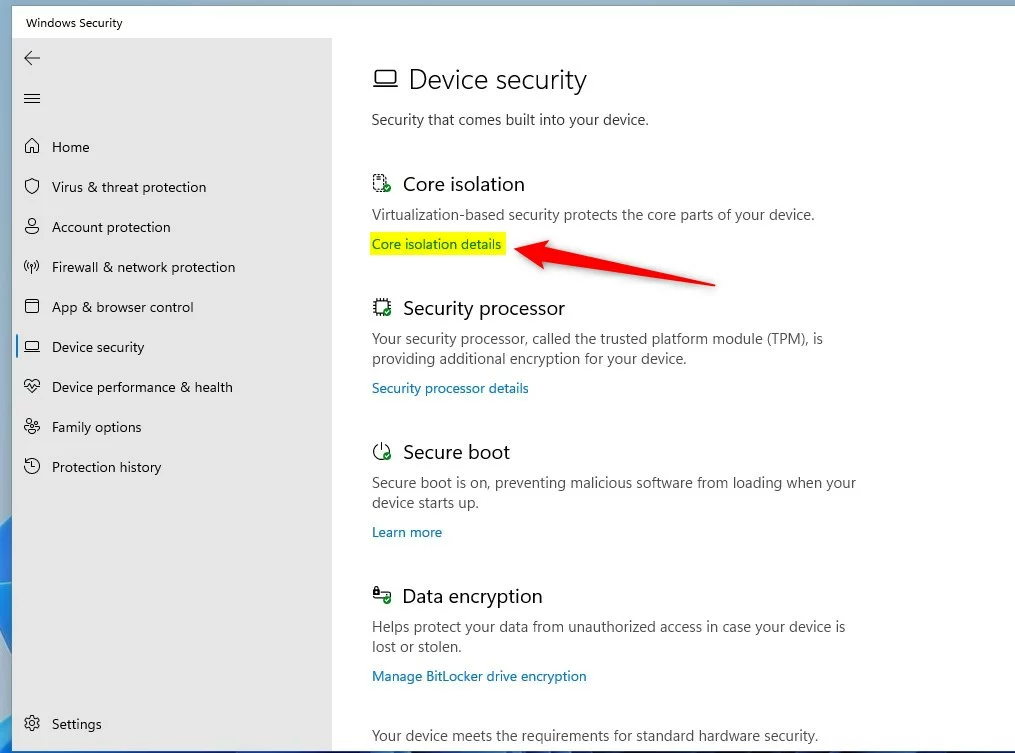
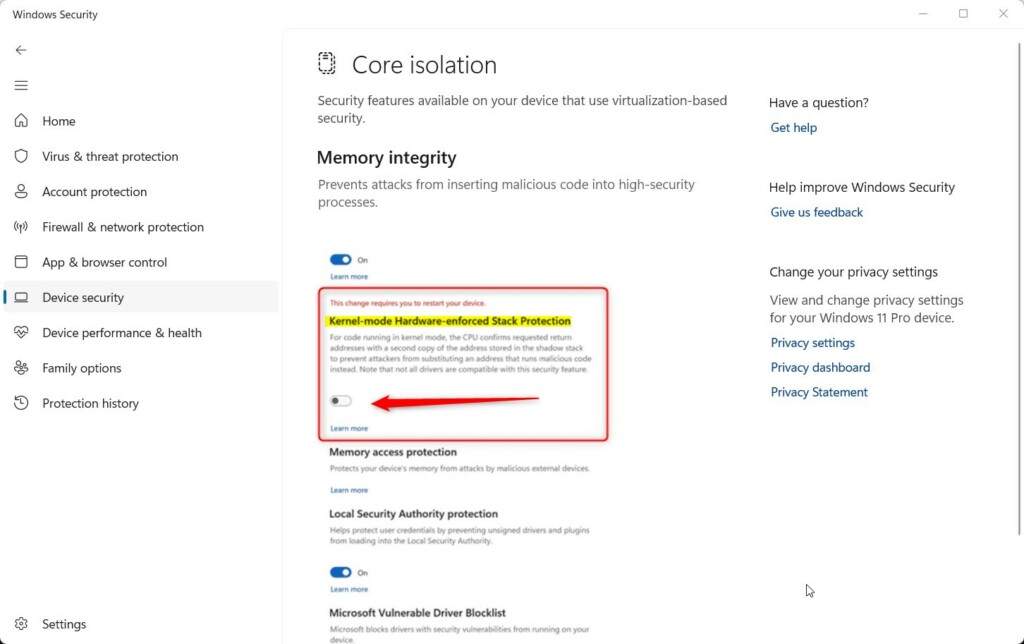
- Turn on (this is the default) or off Kernel-mode Hardware-enforced Stack Protection. Choose what you want.
Note: The Kernel-mode Hardware-enforced Stack Protection setting will be grayed out and disabled if Memory Integrity is turned off.
- [REQUIRES ADMIN] If prompted by UAC, click Yes to approve.
- Restart your computer to apply the change.
Option Two: Use Registry Editor
Turn Kernel-mode Hardware-enforced Stack Protection On or Off Using Commands
Open the Terminal app as administrator and run the command below. [REQUIRES ADMIN]
Turn On Kernel-mode Hardware-enforced Stack Protection
This is the default setting. This will also turn on the required Memory Integrity feature.
reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity" /v Enabled /t REG_DWORD /d 1 /f
reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\KernelShadowStacks" /v Enabled /t REG_DWORD /d 1 /f
reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\KernelShadowStacks" /v WasEnabledBy /t REG_DWORD /d 2 /f
Turn Off Kernel-mode Hardware-enforced Stack Protection
reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\KernelShadowStacks" /v Enabled /t REG_DWORD /d 0 /f
reg delete "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\KernelShadowStacks" /v WasEnabledBy /f
Summary
Kernel-mode Hardware-enforced Stack Protection is a security feature in Windows 11 that protects your computer’s core processes from malware attacks. It works by checking that programs run exactly as intended, using a backup record of correct addresses. When you enable this feature, your computer becomes more secure against advanced attacks. You can turn it on or off using the Windows Security app or through the Terminal app. Remember that your computer needs a compatible CPU, CPU virtualization, and Memory Integrity turned on for this feature to work. After making changes, restart your computer to apply them.


Leave a Reply Cancel reply